Free Dumps, Free Fortinet Dump
Free NSE4_FGT-7.0 Dump
20.Refer to the exhibit.
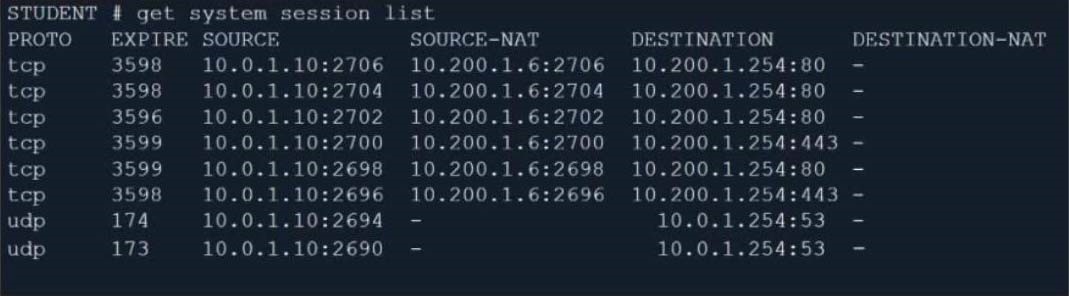
Which contains a session list output. Based on the information shown in the exhibit, which statement is true?
A. Destination NAT is disabled in the firewall policy.
B. One-to-one NAT IP pool is used in the firewall policy.
C. Overload NAT IP pool is used in the firewall policy.
D. Port block allocation IP pool is used in the firewall policy.
21.When configuring a firewall virtual wire pair policy, which following statement is true? A. Any number of virtual wire pairs can be included, as long as the policy traffic direction is the same. B. Only a single virtual wire pair can be included in each policy. C. Any number of virtual wire pairs can be included in each policy, regardless of the policy traffic direction settings. D. Exactly two virtual wire pairs need to be included in each policy.
22.Refer to the exhibit. The Root and To_Internet VDOMs are configured in NAT mode. The DMZ and Local VDOMs are configured in transparent mode. The Root VDOM is the management VDOM. The To_Internet VDOM allows LAN users to access the internet. The To_Internet VDOM is the only VDOM with internet access and is directly connected to ISP modem. With this configuration, which statement is true? A. Inter-VDOM links are required to allow traffic between the Local and Root VDOMs. B. A static route is required on the To_Internet VDOM to allow LAN users to access the internet. C. Inter-VDOM links are required to allow traffic between the Local and DMZ VDOMs. D. Inter-VDOM links are not required between the Root and To_Internet VDOMs because the Root VDOM is used only as a management VDOM.
23.An administrator is configuring an IPsec VPN between site A and site B. The Remote Gateway setting in both sites has been configured as Static IP Address. For site A, the local quick mode selector is 192.168.1.0/24 and the remote quick mode selector is 192.168.2.0/24. Which subnet must the administrator configure for the local quick mode selector for site B? A. 192.168.1.0/24 B. 192.168.0.0/24 C. 192.168.2.0/24 D. 192.168.3.0/24
24.Which CLI command allows administrators to troubleshoot Layer 2 issues, such as an IP address conflict? A. get system status B. get system performance status C. diagnose sys top D. get system arp
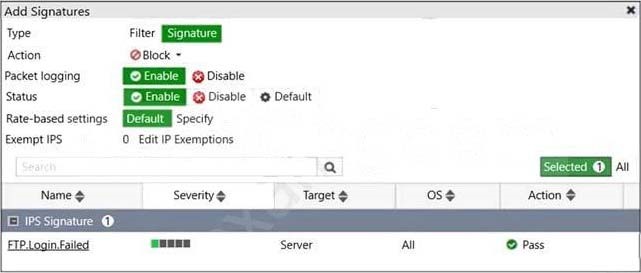
25.Refer to the exhibit. Review the Intrusion Prevention System (IPS) profile signature settings. Which statement is correct in adding the FTP.Login.Failed signature to the IPS sensor profile? A. The signature setting uses a custom rating threshold. B. The signature setting includes a group of other signatures. C. Traffic matching the signature will be allowed and logged. D. Traffic matching the signature will be silently dropped and logged.
26.Which engine handles application control traffic on the next-generation firewall (NGFW) FortiGate? A. Antivirus engine B. Intrusion prevention system engine C. Flow engine D. Detection engine
27.Refer to the exhibit. An administrator is running a sniffer command as shown in the exhibit. Which three pieces of information are included in the sniffer output? (Choose three.) A. Interface name B. Ethernet header C. IP header D. Application header E. Packet payload
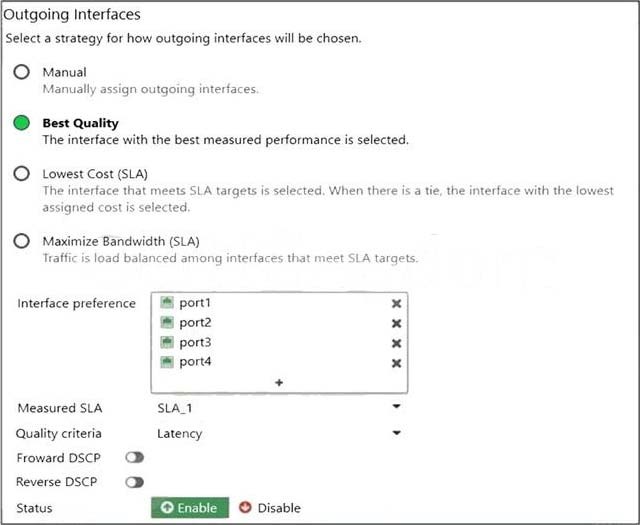
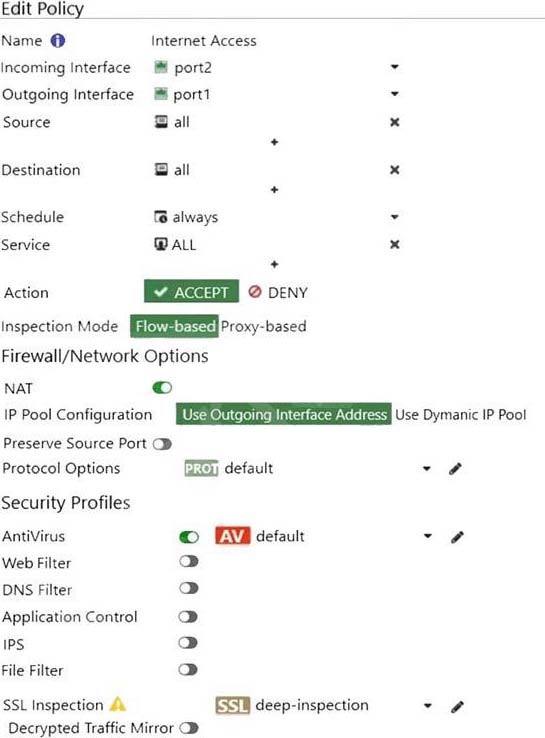
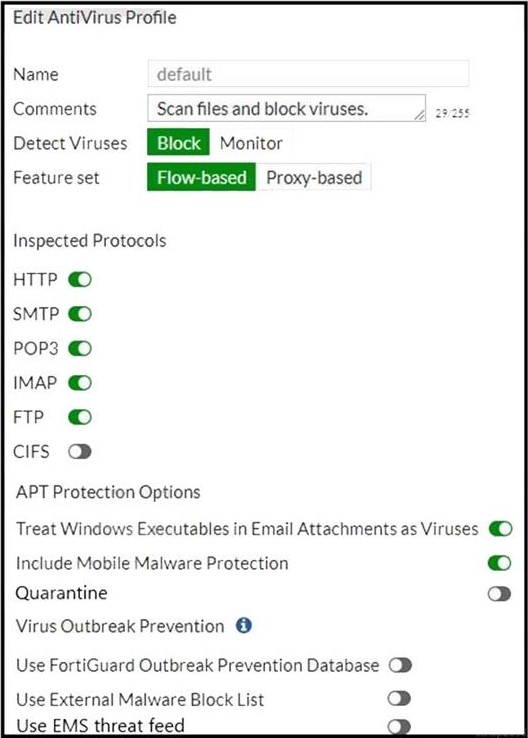
28.Refer to the exhibit. Exhibit A. Exhibit B. The exhibit contains the configuration for an SD-WAN Performance SLA, as well as the output of diagnose sys virtual-wan-link health-check. Which interface will be selected as an outgoing interface? A. port2 B. port4 C. port3 D. port1 29.A network administrator has enabled SSL certificate inspection and antivirus on FortiGate. When downloading an EICAR test file through HTTP, FortiGate detects the virus and blocks the file. When downloading the same file through HTTPS, FortiGate does not detect the virus and the file can be downloaded. What is the reason for the failed virus detection by FortiGate? A. Application control is not enabled B. SSL/SSH Inspection profile is incorrect C. Antivirus profile configuration is incorrect D. Antivirus definitions are not up to date
30.An administrator does not want to report the logon events of service accounts to FortiGate. What setting on the collector agent is required to achieve this? A. Add the support of NTLM authentication. B. Add user accounts to Active Directory (AD). C. Add user accounts to the FortiGate group fitter. D. Add user accounts to the Ignore User List.
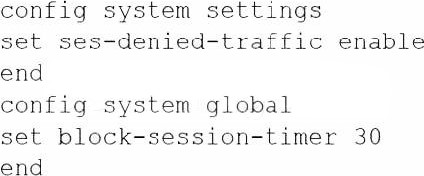
31.An administrator has configured a strict RPF check on FortiGate. Which statement is true about the strict RPF check? A. The strict RPF check is run on the first sent and reply packet of any new session. B. Strict RPF checks the best route back to the source using the incoming interface. C. Strict RPF checks only for the existence of at cast one active route back to the source using the incoming interface. D. Strict RPF allows packets back to sources with all active routes. 32.Which two configuration settings are synchronized when FortiGate devices are in an active-active HA cluster? (Choose two.) A. FortiGuard web filter cache B. FortiGate hostname C. NTP D. DNS 33.An administrator has configured the following settings: What are the two results of this configuration? (Choose two.) A. Device detection on all interfaces is enforced for 30 minutes. B. Denied users are blocked for 30 minutes. C. A session for denied traffic is created. D. The number of logs generated by denied traffic is reduced.
34.Which three options are the remote log storage options you can configure on FortiGate? (Choose three.) A. FortiCache B. FortiSIEM C. FortiAnalyzer D. FortiSandbox E. FortiCloud
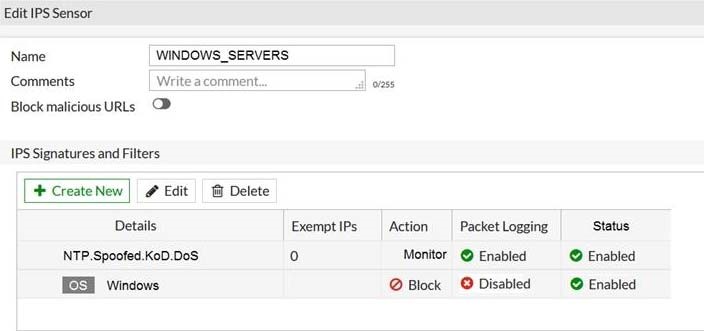
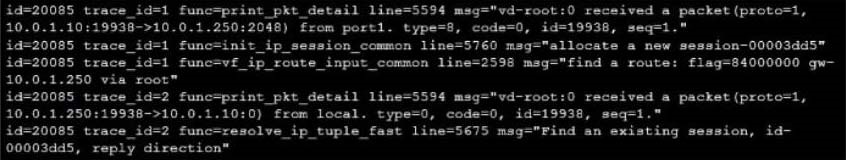
35.Refer to the exhibit. The exhibit shows the IPS sensor configuration. If traffic matches this IPS sensor, which two actions is the sensor expected to take? (Choose two.) A. The sensor will allow attackers matching the NTP.Spoofed.KoD.DoS signature. B. The sensor will block all attacks aimed at Windows servers. C. The sensor will reset all connections that match these signatures. D. The sensor will gather a packet log for all matched traffic. 36.Which statement is correct regarding the inspection of some of the services available by web applications embedded in third-party websites? A. The security actions applied on the web applications will also be explicitly applied on the third-party websites. B. The application signature database inspects traffic only from the original web application server. C. FortiGuard maintains only one signature of each web application that is unique. D. FortiGate can inspect sub-application traffic regardless where it was originated. 37.Refer to the exhibit showing a debug flow output. Which two statements about the debug flow output are correct? (Choose two.) A. The debug flow is of ICMP traffic. B. A firewall policy allowed the connection. C. A new traffic session is created. D. The default route is required to receive a reply.
38.A network administrator wants to set up redundant IPsec VPN tunnels on FortiGate by using two IPsec VPN tunnels and static routes. * All traffic must be routed through the primary tunnel when both tunnels are up * The secondary tunnel must be used only if the primary tunnel goes down * In addition, FortiGate should be able to detect a dead tunnel to speed up tunnel failover Which two key configuration changes are needed on FortiGate to meet the design requirements? (Choose two,) A. Configure a high distance on the static route for the primary tunnel, and a lower distance on the static route for the secondary tunnel. B. Enable Dead Peer Detection. C. Configure a lower distance on the static route for the primary tunnel, and a higher distance on the static route for the secondary tunnel. D. Enable Auto-negotiate and Autokey Keep Alive on the phase 2 configuration of both tunnels.