Free Dumps, Free Fortinet Dump
Free NSE4_FGT-7.0 Dump
Lưu ý: Free NSE4_FGT-7.0 Dump chỉ dành cho mục đích học tập và làm quen với bài thi. Nội dung của Free NSE4_FGT-7.0 Dump không được cập nhật mới nhất nên không đảm bảo Pass Exam. Liên hệ ITexamViet để Pass Exam Nhanh Nhất.
1.How does FortiGate act when using SSL VPN in web mode? A. FortiGate acts as an FDS server.
B. FortiGate acts as an HTTP reverse proxy.
C. FortiGate acts as DNS server.
D. FortiGate acts as router.
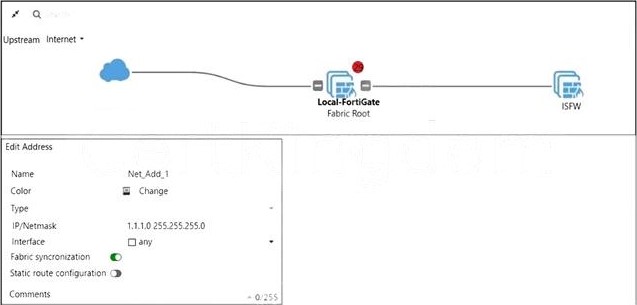
2.Refer to the exhibits. Exhibit A. Exhibit B. An administrator creates a new address object on the root FortiGate (Local-FortiGate) in the security fabric. After synchronization, this object is not available on the downstream FortiGate (ISFW). What must the administrator do to synchronize the address object? A. Change the csf setting on Local-FortiGate (root) to sec configuration-sync local. B. Change the csf setting on ISFW (downstream) to sec configuracion-sync local. C. Change the csf setting on Local-FortiGate (root) to sec fabric-objecc-unificacion defaulc. D. Change the csf setting on ISFW (downstream) to sec fabric-objecc-unificacion defaulc.
3.Refer to the exhibit. Given the security fabric topology shown in the exhibit, which two statements are true? (Choose two.) A. There are five devices that are part of the security fabric. B. Device detection is disabled on all FortiGate devices. C. This security fabric topology is a logical topology view. D. There are 19 security recommendations for the security fabric.
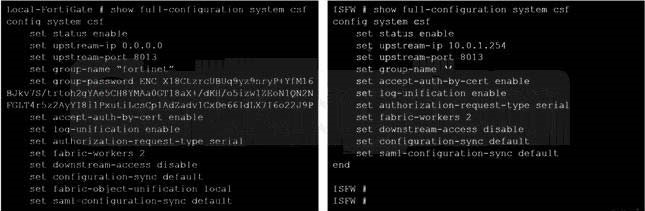
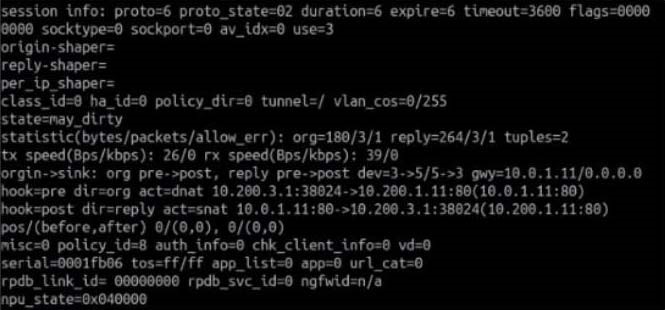
4.Refer to the exhibit. Exhibit A. Exhibit B. The exhibit contains a network diagram, virtual IP, IP pool, and firewall policies configuration. The WAN (port1) interface has the IP address 10.200.1.1/24. The LAN (port3) interface has the IP address 10 .0.1.254. /24. The first firewall policy has NAT enabled using IP Pool. The second firewall policy is configured with a VIP as the destination address. Which IP address will be used to source NAT the internet traffic coming from a workstation with the IP address 10.0.1.10? A. 10.200.1.1 B. 10.200.3.1 C. 10.200.1.100 D. 10.200.1.10
5.Which statement about video filtering on FortiGate is true? A. Full SSL Inspection is not required. B. It is available only on a proxy-based firewall policy. C. It inspects video files hosted on file sharing services. D. Video filtering FortiGuard categories are based on web filter FortiGuard categories.
6.Which two statements about FortiGate FSSO agentless polling mode are true? (Choose two.) A. FortiGate uses the AD server as the collector agent. B. FortiGate uses the SMB protocol to read the event viewer logs from the DCs. C. FortiGate does not support workstation check. D. FortiGate directs the collector agent to use a remote LDAP server.
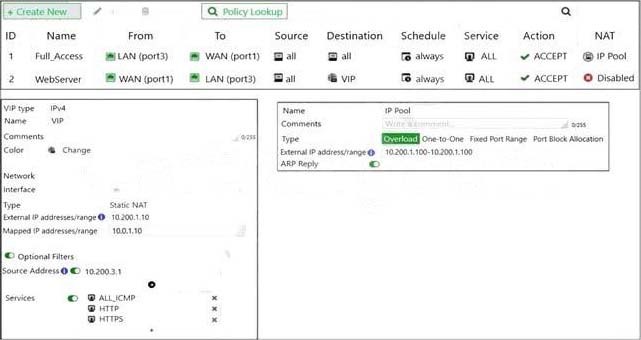
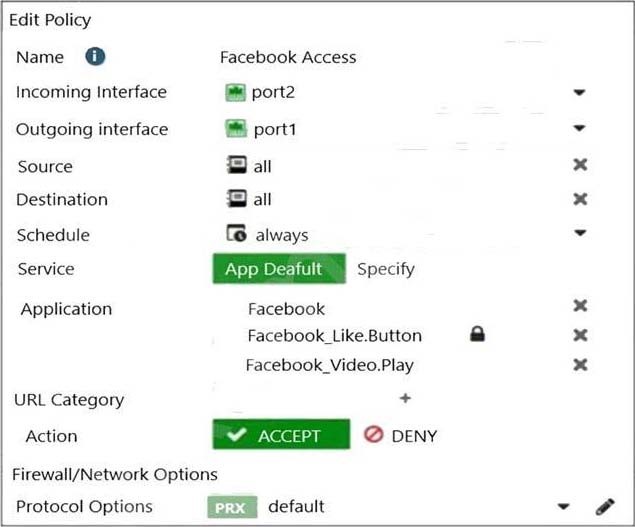
7.Which two statements are correct about SLA targets? (Choose two.) A. You can configure only two SLA targets per one Performance SLA. B. SLA targets are optional. C. SLA targets are required for SD-WAN rules with a Best Quality strategy. D. SLA targets are used only when referenced by an SD-WAN rule. 8.Refer to the exhibits. Exhibit A. Exhibit B. The exhibits show the SSL and authentication policy (Exhibit A) and the security policy (Exhibit B) tor Facebook. Users are given access to the Facebook web application. They can play video content hosted on Facebook but they are unable to leave reactions on videos or other types of posts. Which part of the policy configuration must you change to resolve the issue? A. The SSL inspection needs to be a deep content inspection. B. Force access to Facebook using the HTTP service. C. Additional application signatures are required to add to the security policy. D. Add Facebook in the URL category in the security policy.
9.Which two attributes are required on a certificate so it can be used as a CA certificate on SSL Inspection? (Choose two.) A. The keyUsage extension must be set to keyCertSign. B. The common name on the subject field must use a wildcard name. C. The issuer must be a public CA. D. The CA extension must be set to TRUE.
10.An administrator wants to configure Dead Peer Detection (DPD) on IPSEC VPN for detecting dead tunnels. The requirement is that FortiGate sends DPD probes only when no traffic is observed in the tunnel. Which DPD mode on FortiGate will meet the above requirement? A. Disabled B. On Demand C. Enabled D. On Idle 11.Which two statements about antivirus scanning mode are true? (Choose two.) A. In proxy-based inspection mode, files bigger than the buffer size are scanned. B. In flow-based inspection mode, FortiGate buffers the file, but also simultaneously transmits it to the client. C. In proxy-based inspection mode, antivirus scanning buffers the whole file for scanning, before sending it to the client. D. In flow-based inspection mode, files bigger than the buffer size are scanned.
12.FortiGuard categories can be overridden and defined in different categories. To create a web rating override for example.com home page, the override must be configured using a specific syntax. Which two syntaxes are correct to configure web rating for the home page? (Choose two.) A. www.example.com:443 B. www.example.com C. example.com D. www.example.com/index.html
13.Which two statements are correct about NGFW Policy-based mode? (Choose two.) A. NGFW policy-based mode does not require the use of central source NAT policy B. NGFW policy-based mode can only be applied globally and not on individual VDOMs C. NGFW policy-based mode supports creating applications and web filtering categories directly in a firewall policy D. NGFW policy-based mode policies support only flow inspection
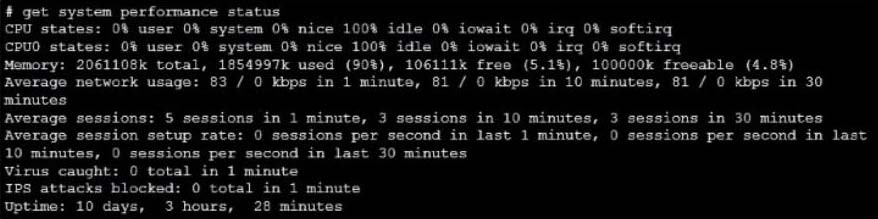
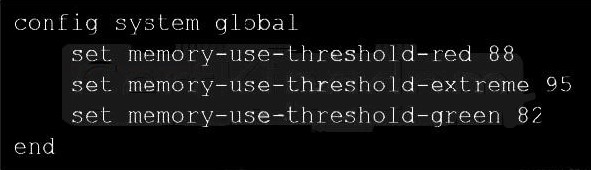
14.Refer to the exhibits. Exhibit A shows system performance output. Exhibit B shows s FortiGate configured with the default configuration of high memory usage thresholds. Based on the system performance output, which two statements are correct? (Choose two.) A. Administrators can access FortiGate only through the console port. B. FortiGate has entered conserve mode. C. FortiGate will start sending all files to FortiSandbox for inspection. D. Administrators cannot change the configuration.
15.Why does FortiGate Keep TCP sessions in the session table for several seconds, even after both sides (client and server) have terminated the session? A. To allow for out-of-order packets that could arrive after the FIN/ACK packets B. To finish any inspection operations C. To remove the NAT operation D. To generate logs
16.Which two statements are true about the FGCP protocol? (Choose two.) A. Not used when FortiGate is in Transparent mode B. Elects the primary FortiGate device C. Runs only over the heartbeat links D. Is used to discover FortiGate devices in different HA groups
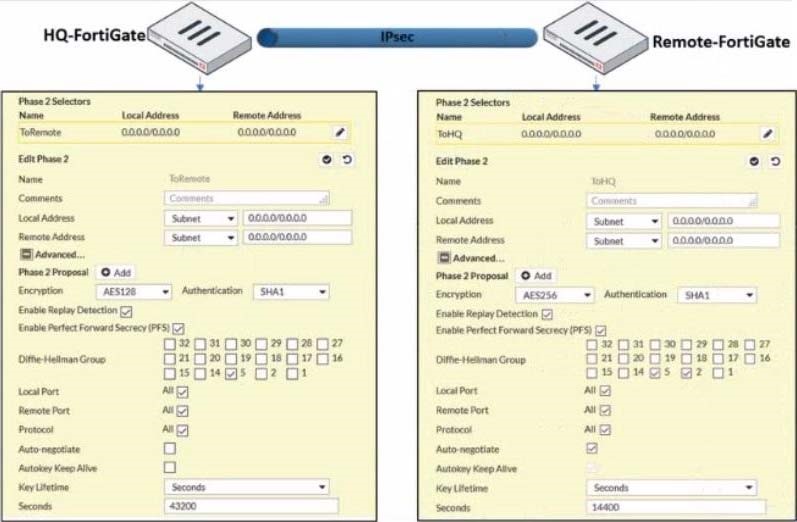
17.Refer to the exhibit. A network administrator is troubleshooting an IPsec tunnel between two FortiGate devices. The administrator has determined that phase 1 status is up. but phase 2 fails to come up. Based on the phase 2 configuration shown in the exhibit, what configuration change will bring phase 2 up? A. On HQ-FortiGate, enable Auto-negotiate. B. On Remote-FortiGate, set Seconds to 43200. C. On HQ-FortiGate, enable Diffie-Hellman Group 2. D. On HQ-FortiGate, set Encryption to AES256.
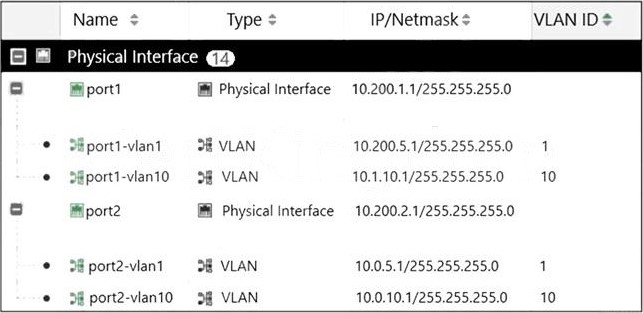
18.Refer to the exhibit. Given the interfaces shown in the exhibit, which two statements are true? (Choose two.) A. Traffic between port2 and port2-vlan1 is allowed by default. B. port1-vlan10 and port2-vlan10 are part of the same broadcast domain. C. port1 is a native VLAN. D. port1-vlan and port2-vlan1 can be assigned in the same VDOM or to different VDOMs.